The Strategic Intelligence File concerning identifiers 935973674, 662988831, 8002965598, 928308752, 667020531, and 722399102 presents a structured approach to data analysis. It systematically uncovers patterns and relationships that inform critical decision-making processes. This repository offers insights that could significantly influence risk management strategies. However, the implications of these findings remain to be fully explored, raising questions about their potential impact on security frameworks and individual freedoms.
Overview of the Identifiers
Identifiers serve as crucial components within the realm of strategic intelligence, acting as unique markers that facilitate the categorization and retrieval of information.
Their significance lies in their ability to unveil underlying data patterns, enabling analysts to discern relationships and trends.
Data Analysis and Insights
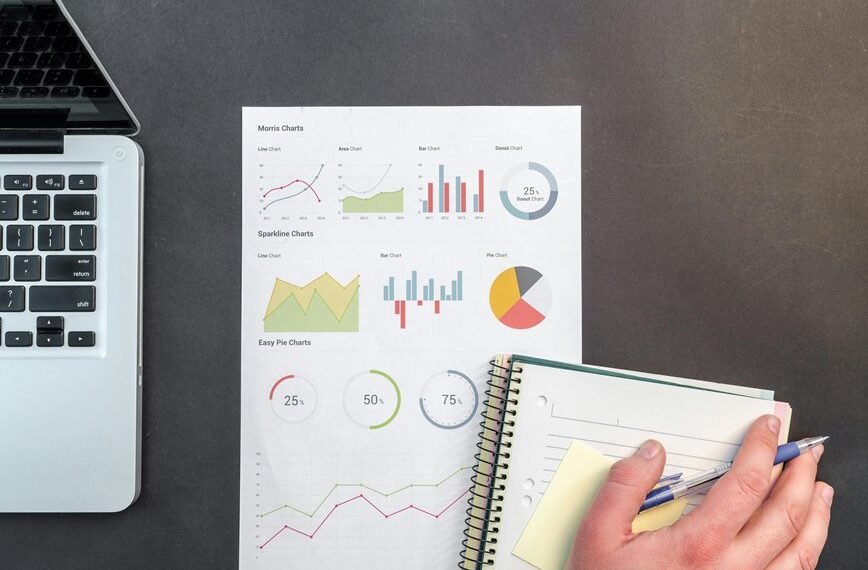
Data analysis serves as the backbone of strategic intelligence, transforming raw information into actionable insights.
By employing various analytical methods, practitioners can identify critical data trends that inform decision-making processes. This structured approach enables stakeholders to harness information effectively, facilitating the attainment of strategic objectives.
Ultimately, the synthesis of data trends through rigorous analysis empowers individuals to exercise informed freedom in their strategic endeavors.
Implications for Strategic Intelligence
While the analysis of data provides a foundation for informed decision-making, its broader implications for strategic intelligence extend far beyond mere insights.
Intelligence frameworks must evolve to accommodate these findings, enabling more nuanced strategic assessments. This adaptation fosters agility, allowing organizations to navigate complexities and uncertainties, ultimately empowering them to leverage intelligence effectively in pursuit of their objectives and safeguarding their interests.
Applications in Risk Management and Security
The evolution of intelligence frameworks significantly influences applications in risk management and security. Enhanced risk assessment techniques and robust threat detection capabilities enable organizations to implement effective security frameworks.
These frameworks prioritize data privacy and incorporate compliance measures, ensuring adherence to regulations.
Furthermore, continuous vulnerability analysis strengthens resilience against emerging threats, fostering a proactive approach in safeguarding assets while promoting individual freedoms within secure environments.
Conclusion
In conclusion, the Strategic Intelligence File serves as a beacon, illuminating the intricate web of relationships among the identifiers. By distilling raw data into strategic insights, it empowers organizations akin to skilled navigators charting a course through turbulent waters. The implications for risk management and security are profound, enabling a proactive stance against emerging threats while safeguarding individual freedoms. As the complexities of the modern landscape evolve, this repository remains a vital tool for informed decision-making and resilient frameworks.